A Company Wants to Plan a Stateoftheart Information and Operating System to Enable
Introduction to Networks ( Version seven.00) – Modules 16 – 17: Building and Securing a Small Network Exam
1. Which component is designed to protect against unauthorized communications to and from a estimator?
- security center
- port scanner
- antimalware
- antivirus
- firewall
2. Which command volition cake login attempts on RouterA for a menstruum of thirty seconds if at that place are 2 failed login attempts within 10 seconds?
- RouterA(config)# login block-for 10 attempts ii inside 30
- RouterA(config)# login block-for 30 attempts 2 within 10
- RouterA(config)# login block-for ii attempts 30 within 10
- RouterA(config)# login block-for 30 attempts x within 2
3. What is the purpose of the network security accounting function?
- to crave users to prove who they are
- to determine which resources a user can access
- to continue track of the deportment of a user
- to provide challenge and response questions
4. What type of set on may involve the use of tools such equally nslookup and fping?
- access attack
- reconnaissance attack
- denial of service assail
- worm set on
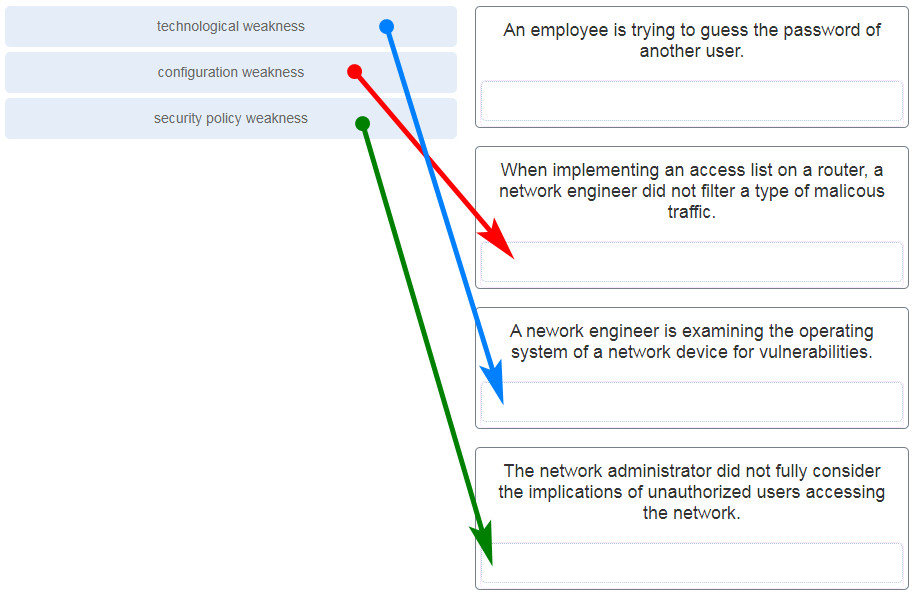
5. Lucifer each weakness with an instance. (Not all options are used.)
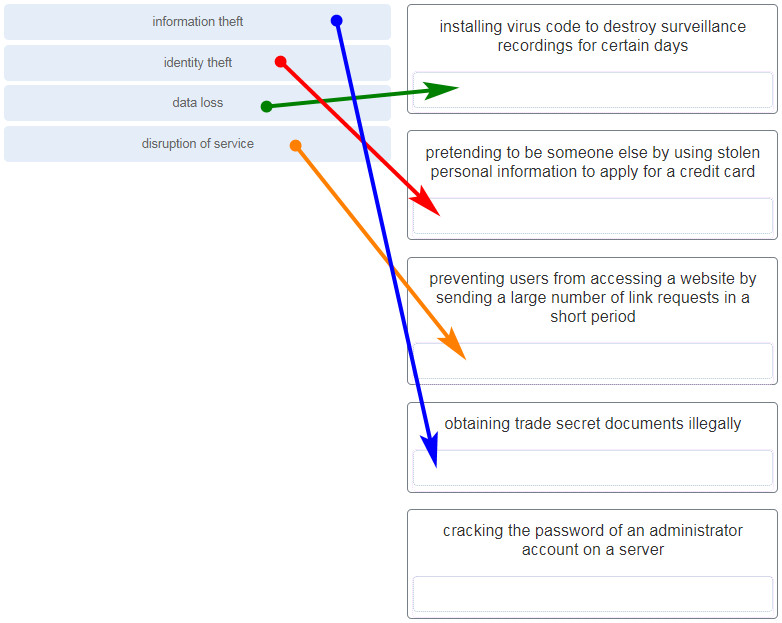
6. Match the type of data security threat to the scenario. (Non all options are used.)
7. Which case of malicious code would be classified equally a Trojan horse?
- malware that was written to look like a video game
- malware that requires manual user intervention to spread between systems
- malware that attaches itself to a legitimate program and spreads to other programs when launched
- malware that can automatically spread from ane system to some other past exploiting a vulnerability in the target
8. What is the difference between a virus and a worm?
- Viruses self-replicate but worms do not.
- Worms self-replicate merely viruses do not.
- Worms require a host file but viruses practice not.
- Viruses hibernate in legitimate programs but worms do not.
9. Which set on involves a compromise of information that occurs betwixt two finish points?
- denial-of-service
- human being-in-the-middle set on
- extraction of security parameters
- username enumeration
10. Which type of assault involves an antagonist attempting to get together information about a network to identify vulnerabilities?
- reconnaissance
- DoS
- dictionary
- man-in-the-centre
11. Match the description to the blazon of firewall filtering. (Not all options are used.)

12. What is the purpose of the network security authentication function?
- to crave users to prove who they are
- to make up one's mind which resources a user can access
- to keep track of the actions of a user
- to provide claiming and response questions
13. Which firewall feature is used to ensure that packets coming into a network are legitimate responses to requests initiated from internal hosts?
- stateful package inspection
- URL filtering
- application filtering
- packet filtering
14. When applied to a router, which command would help mitigate creature-force password attacks against the router?
- exec-timeout thirty
- service password-encryption
- banner motd $Max failed logins = 5$
- login block-for 60 attempts 5 inside lx
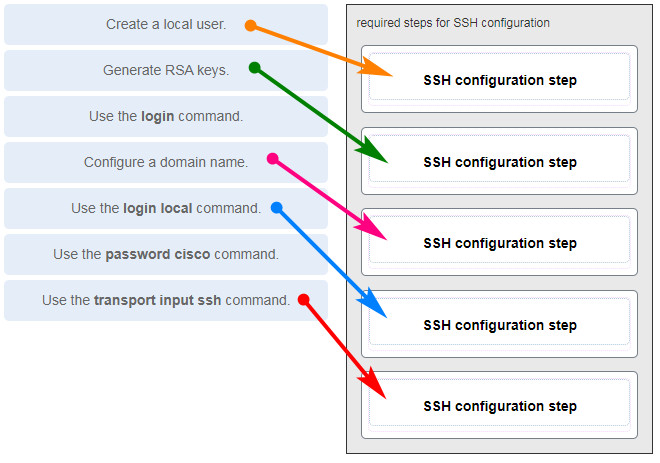
15. Identify the steps needed to configure a switch for SSH. The reply order does not matter. (Not all options are used.)
xvi. What characteristic of SSH makes information technology more than secure than Telnet for a device management connexion?
- confidentiality with IPsec
- stronger countersign requirement
- random one-time port connectedness
- login information and information encryption
17. What is the advantage of using SSH over Telnet?
- SSH is easier to use.
- SSH operates faster than Telnet.
- SSH provides secure communications to access hosts.
- SSH supports authentication for a connexion asking.
eighteen. What is the role of an IPS?
- detecting and blocking of attacks in real time
- connecting global threat data to Cisco network security devices
- authenticating and validating traffic
- filtering of nefarious websites
19. A user is redesigning a network for a minor company and wants to ensure security at a reasonable toll. The user deploys a new application-enlightened firewall with intrusion detection capabilities on the ISP connectedness. The user installs a 2nd firewall to separate the company network from the public network. Additionally, the user installs an IPS on the internal network of the company. What arroyo is the user implementing?
- attack based
- risk based
- structured
- layered
20. What is an accurate description of redundancy?
- configuring a router with a consummate MAC address database to ensure that all frames can be forwarded to the correct destination
- configuring a switch with proper security to ensure that all traffic forwarded through an interface is filtered
- designing a network to apply multiple virtual devices to ensure that all traffic uses the best path through the internetwork
- designing a network to use multiple paths between switches to ensure in that location is no single indicate of failure
21. A network administrator is upgrading a modest business network to give loftier priority to real-fourth dimension applications traffic. What two types of network services is the network administrator trying to accommodate? (Choose 2.)
- phonation
- video
- instant messaging
- FTP
- SNMP
22. What is the purpose of a pocket-size company using a protocol analyzer utility to capture network traffic on the network segments where the company is considering a network upgrade?
- to place the source and destination of local network traffic
- to capture the Internet connection bandwidth requirement
- to certificate and analyze network traffic requirements on each network segment
- to establish a baseline for security analysis after the network is upgraded
23. Refer to the showroom. An ambassador is testing connectivity to a remote device with the IP address 10.1.ane.1. What does the output of this control indicate?
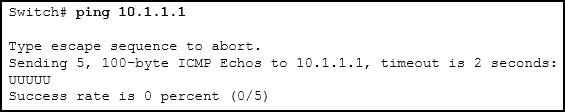
- Connectivity to the remote device was successful.
- A router forth the path did not accept a route to the destination.
- A ping bundle is beingness blocked by a security device forth the path.
- The connection timed out while waiting for a reply from the remote device.
24. Which method is used to send a ping message specifying the source accost for the ping?
- Consequence the ping command from inside interface configuration fashion.
- Issue the ping command without specifying a destination IP address.
- Consequence the ping command without extended commands.
- Issue the ping command afterward shutting downward united nations-needed interfaces.
25. A network engineer is analyzing reports from a recently performed network baseline. Which situation would describe a possible latency event?
- a change in the bandwidth according to the bear witness interfaces output
- a next-hop timeout from a traceroute
- an increase in host-to-host ping response times
- a change in the amount of RAM co-ordinate to the show version output
26. Which argument is true near Cisco IOS ping indicators?
- '!' indicates that the ping was unsuccessful and that the device may take issues finding a DNS server.
- 'U' may betoken that a router along the path did non contain a road to the destination accost and that the ping was unsuccessful.
- '.' indicates that the ping was successful but the response time was longer than normal.
- A combination of '.' and '!' indicates that a router along the path did not have a road to the destination address and responded with an ICMP unreachable message.
27. A user reports a lack of network connectivity. The technician takes control of the user auto and attempts to ping other computers on the network and these pings fail. The technician pings the default gateway and that besides fails. What can be adamant for sure by the results of these tests?
- The NIC in the PC is bad.
- The TCP/IP protocol is not enabled.
- The router that is fastened to the same network as the workstation is downwards.
- Nothing can be determined for certain at this point.
28. A network technician issues the C:\> tracert -half dozen world wide web.cisco.com control on a Windows PC. What is the purpose of the -half dozen command selection?
- Information technology forces the trace to use IPv6.
- It limits the trace to only 6 hops.
- It sets a 6 milliseconds timeout for each replay.
- It sends 6 probes within each TTL fourth dimension menstruation.
29. Why would a network administrator utilize the tracert utility?
- to determine the active TCP connections on a PC
- to cheque information nigh a DNS name in the DNS server
- to identify where a parcel was lost or delayed on a network
- to display the IP address, default gateway, and DNS server address for a PC
xxx. A ping fails when performed from router R1 to directly connected router R2. The network administrator then gain to issue the bear witness cdp neighbors command. Why would the network administrator event this command if the ping failed between the ii routers?
- The network administrator suspects a virus because the ping command did non work.
- The network administrator wants to verify Layer ii connectivity.
- The network administrator wants to verify the IP address configured on router R2.
- The network administrator wants to determine if connectivity can exist established from a non-direct connected network.
31. A network engineer is troubleshooting connectivity issues amongst interconnected Cisco routers and switches. Which command should the engineer employ to find the IP accost information, host name, and IOS version of neighboring network devices?
- evidence version
- prove ip route
- evidence interfaces
- show cdp neighbors detail
32. What information about a Cisco router can be verified using the show version control?
- the routing protocol version that is enabled
- the value of the configuration register
- the operational condition of serial interfaces
- the administrative distance used to reach networks
33. Which command should be used on a Cisco router or switch to let log messages to be displayed on remotely connected sessions using Telnet or SSH?
- debug all
- logging synchronous
- evidence running-config
- terminal monitor
34. Which control can an administrator issue on a Cisco router to send debug messages to the vty lines?
- last monitor
- logging console
- logging buffered
- logging synchronous
35. Past post-obit a structured troubleshooting approach, a network ambassador identified a network outcome after a conversation with the user. What is the next step that the administrator should accept?
- Verify full system functionality.
- Examination the theory to decide cause.
- Found a theory of likely causes.
- Constitute a plan of action to resolve the effect.
36. Users are complaining that they are unable to browse certain websites on the Net. An administrator tin can successfully ping a spider web server via its IP address, but cannot scan to the domain proper noun of the website. Which troubleshooting tool would exist most useful in determining where the problem is?
- netstat
- tracert
- nslookup
- ipconfig
37. An employee complains that a Windows PC cannot connect to the Cyberspace. A network technician issues the ipconfig command on the PC and is shown an IP address of 169.254.10.3. Which two conclusions can be drawn? (Cull ii.)
- The PC cannot contact a DHCP server.
- The DNS server accost is misconfigured.
- The default gateway address is not configured.
- The PC is configured to obtain an IP address automatically.
- The enterprise network is misconfigured for dynamic routing.
38. Refer to the exhibit. Host H3 is having trouble communicating with host H1. The network administrator suspects a trouble exists with the H3 workstation and wants to prove that there is no trouble with the R2 configuration. What tool could the network administrator use on router R2 to prove that communication exists to host H1 from the interface on R2, which is the interface that H3 uses when communicating with remote networks?
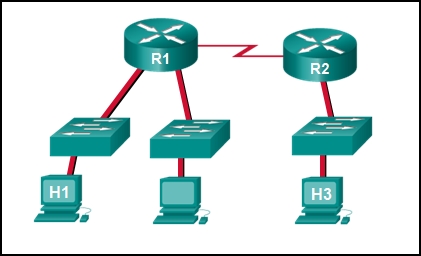
-
traceroute -
show cdp neighbors - Telnet
- an extended ping
39. Refer to the exhibit. Baseline documentation for a small company had ping round trip time statistics of 36/97/132 between hosts H1 and H3. Today the network administrator checked connectivity by pinging between hosts H1 and H3 that resulted in a circular trip time of 1458/2390/6066. What does this signal to the network administrator?
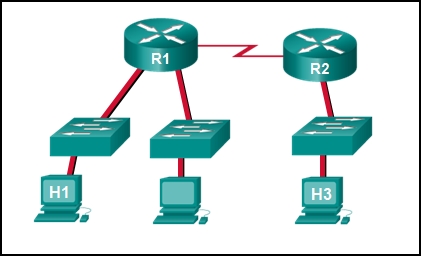
- Connectivity betwixt H1 and H3 is fine.
- H3 is not continued properly to the network.
- Something is causing interference between H1 and R1.
- Performance betwixt the networks is within expected parameters.
- Something is causing a time delay between the networks.
40. Which network service automatically assigns IP addresses to devices on the network?
- DHCP
- Telnet
- DNS
- traceroute
41. Which command can an administrator execute to decide what interface a router will use to reach remote networks?
- show arp
- show interfaces
- show ip route
- show protocols
42. On which two interfaces or ports can security be improved by configuring executive timeouts? (Choose two.)
- Fast Ethernet interfaces
- console ports
- serial interfaces
- vty ports
- loopback interfaces
43. When configuring SSH on a router to implement secure network management, a network engineer has issued the login local and transport input ssh line vty commands. What iii additional configuration deportment have to be performed to consummate the SSH configuration? (Choose three.)
- Set the user privilege levels.
- Generate the asymmetric RSA keys.
- Configure the correct IP domain name.
- Configure role-based CLI access.
- Create a valid local username and password database.
- Manually enable SSH after the RSA keys are generated.
44. What is considered the most effective way to mitigate a worm attack?
- Change organisation passwords every 30 days.
- Ensure that all systems have the virtually current virus definitions.
- Ensure that AAA is configured in the network.
- Download security updates from the operating system vendor and patch all vulnerable systems.
45. Which statement describes the ping and tracert commands?
- Tracert shows each hop, while ping shows a destination reply merely.
- Tracert uses IP addresses; ping does not.
- Both ping and tracert can show results in a graphical display.
- Ping shows whether the transmission is successful; tracert does not.
46. A technician is to certificate the electric current configurations of all network devices in a higher, including those in off-site buildings. Which protocol would be best to apply to securely access the network devices?
- FTP
- HTTP
- SSH
- Telnet
47. Open the PT Activity. Perform the tasks in the activity instructions and and then reply the question.
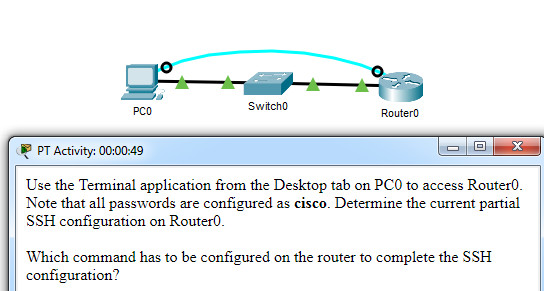
CCNA 1 v7 Modules 16 – 17 Building and Securing a Small Network Examination
Which command has to be configured on the router to complete the SSH configuration?
- service password-encryption
- transport input ssh
- enable undercover class
- ip domain-name cisco.com
48. An administrator decides to use "WhatAreyouwaiting4" as the password on a newly installed router. Which argument applies to the password choice?
- It is strong because it uses a passphrase.
- It is weak because it is often the default countersign on new devices.
- It is weak since it uses easily found personal information.
- It is weak since it is a word that is easily found in the dictionary.
49. An administrator decides to employ "pR3s!d7n&0" as the password on a newly installed router. Which statement applies to the countersign choice?
- It is stiff because information technology uses a minimum of 10 numbers, letters and special characters.
- It is weak because it is often the default password on new devices.
- It is weak since it uses easily found personal information.
- It is weak since it is a word that is easily found in the dictionary.
50. An ambassador decides to use "v$vii*4#033!" equally the password on a newly installed router. Which statement applies to the password pick?
- It is strong because information technology contains 10 numbers and special characters.
- It is weak because it is often the default password on new devices.
- It is weak since information technology uses easily found personal data.
- It is strong considering information technology uses a minimum of 10 numbers, letters and special characters.
51. An administrator decides to use "pR3s!d7n&0" as the countersign on a newly installed router. Which statement applies to the countersign choice?
- It is stiff because it uses a minimum of ten numbers, letters and special characters.
- Information technology is weak since information technology is a word that is easily found in the dictionary.
- It is strong because it uses a passphrase.
- It is potent considering information technology contains 10 numbers and special characters.
52. An ambassador decides to use "12345678!" as the password on a newly installed router. Which statement applies to the password choice?
- It is weak considering it uses a series of numbers or letters.
- It is strong because information technology uses a passphrase.
- It is weak since it is a word that is easily found in the dictionary.
- It is strong because it uses a minimum of ten numbers, letters and special characters.
53. An ambassador decides to utilize "admin" as the countersign on a newly installed router. Which statement applies to the countersign pick?
- Information technology is weak because it is frequently the default countersign on new devices.
- It is strong because it uses a passphrase.
- It is strong because it uses a minimum of 10 numbers, messages and special characters.
- It is potent because it contains 10 numbers and special characters.
54. An administrator decides to use "Feb121978" as the password on a newly installed router. Which statement applies to the password option?
- It is weak because information technology uses easily constitute personal information.
- It is strong considering it uses a passphrase.
- It is weak since it is a give-and-take that is easily found in the dictionary.
- Information technology is strong because it uses a minimum of ten numbers, letters and special characters.
55. An administrator decides to use "password" as the password on a newly installed router. Which statement applies to the password choice?
- It is weak considering it is a usually used password.
- It is weak since it is a word that is easily establish in the lexicon.
- It is strong considering it uses a passphrase.
- It is strong because it uses a minimum of 10 numbers, letters and special characters.
56. An administrator decides to use "RobErT" equally the password on a newly installed router. Which argument applies to the password choice?
- It is weak since it uses easily found personal information.
- It is strong because it uses a passphrase.
- It is strong because information technology uses a minimum of x numbers, messages and special characters.
- It is strong because it contains 10 numbers and special characters.
57. An ambassador decides to use "Elizabeth" every bit the password on a newly installed router. Which statement applies to the countersign pick?
- It is weak considering it uses easily plant personal information.
- It is potent because information technology uses a passphrase.
- It is weak since it is a discussion that is easily establish in the lexicon.
- It is strong because it uses a minimum of 10 numbers, messages and special characters.
Rules for strong passwords:
* minimum of eight characters, preferably 10.
* use complex combinations of numbers, special characters, and upper and lower instance letters.
* avert repetition, common dictionary words, letter or number sequences.
* avoid names of children, relatives, pets, birthdays, or any easily identifiable personal information.
* can be created past misspelling words or replacing vowels with numbers or special characters.
58. A network technician is troubleshooting an outcome and needs to verify the IP addresses of all interfaces on a router. What is the all-time control to use to accomplish the task?
- testify ip interface brief
- nslookup
- ipconfig getifaddr en0
- show ip road
59. Students who are connected to the same switch are having slower than normal response times. The administrator suspects a duplex setting event. What is the all-time control to employ to accomplish the task?
- show interfaces
- ipconfig getifaddr en0
- copy running-config startup-config
- show ip nat translations
60. A user wants to know the IP address of the PC. What is the best control to use to reach the task?
- ipconfig
- re-create running-config startup-config
- testify interfaces
- show ip nat translations
61. A pupil wants to save a router configuration to NVRAM. What is the best control to utilize to accomplish the task?
- copy running-config startup-config
- testify interfaces
- show ip nat translations
- bear witness ip road
62. A support technician needs to know the IP address of the wireless interface on a MAC. What is the best command to use to accomplish the job?
- ipconfig getifaddr en0
- copy running-config startup-config
- show interfaces
- prove ip nat translations
63. A network technician is troubleshooting an issue and needs to verify all of the IPv6 interface addresses on a router. What is the best command to use to accomplish the job?
- show ipv6 interface
- show interfaces
- show ip nat translations
- show ip route
64. A instructor is having difficulties connecting his PC to the classroom network. He needs to verify that a default gateway is configured correctly. What is the best command to utilise to attain the task?
- ipconfig
- re-create running-config startup-config
- testify interfaces
- evidence ip nat translations
65. But employees connected to IPv6 interfaces are having difficulty connecting to remote networks. The analyst wants to verify that IPv6 routing has been enabled. What is the all-time command to use to attain the task?
- show running-config
- evidence interfaces
- re-create running-config startup-config
- testify ip nat translations
66. An administrator is troubleshooting connectivity bug and needs to determine the IP address of a website. What is the all-time command to utilize to accomplish the task?
- nslookup
- bear witness ipv6 route
- show ipv6 interface
- copy startup-config running-config
67. But employees connected to IPv6 interfaces are having difficulty connecting to remote networks. The analyst wants to verify that IPv6 routing has been enabled. What is the all-time command to utilize to reach the task?
- show running-config
- evidence ipv6 route
- bear witness ipv6 interface
- copy startup-config running-config
68. What is a characteristic of UDP?
- UDP datagrams take the aforementioned path and get in in the correct order at the destination.
- Applications that utilize UDP are always considered unreliable.
- UDP reassembles the received datagrams in the club they were received.
- UDP only passes data to the network when the destination is fix to receive the data.
connollytheraid1969.blogspot.com
Source: https://itexamanswers.net/ccna-1-v7-modules-16-17-building-and-securing-a-small-network-exam-answers.html
0 Response to "A Company Wants to Plan a Stateoftheart Information and Operating System to Enable"
Post a Comment